Senior Vibe Coder dealing with security
You know that senior developer on your team — the one who's been shipping code since jQuery was revolutionary? They can architect a distributed system in their sleep, but ask them about Content Securi...

Enjoy this article? Clap on Medium or like on Substack to help it reach more people 🙏
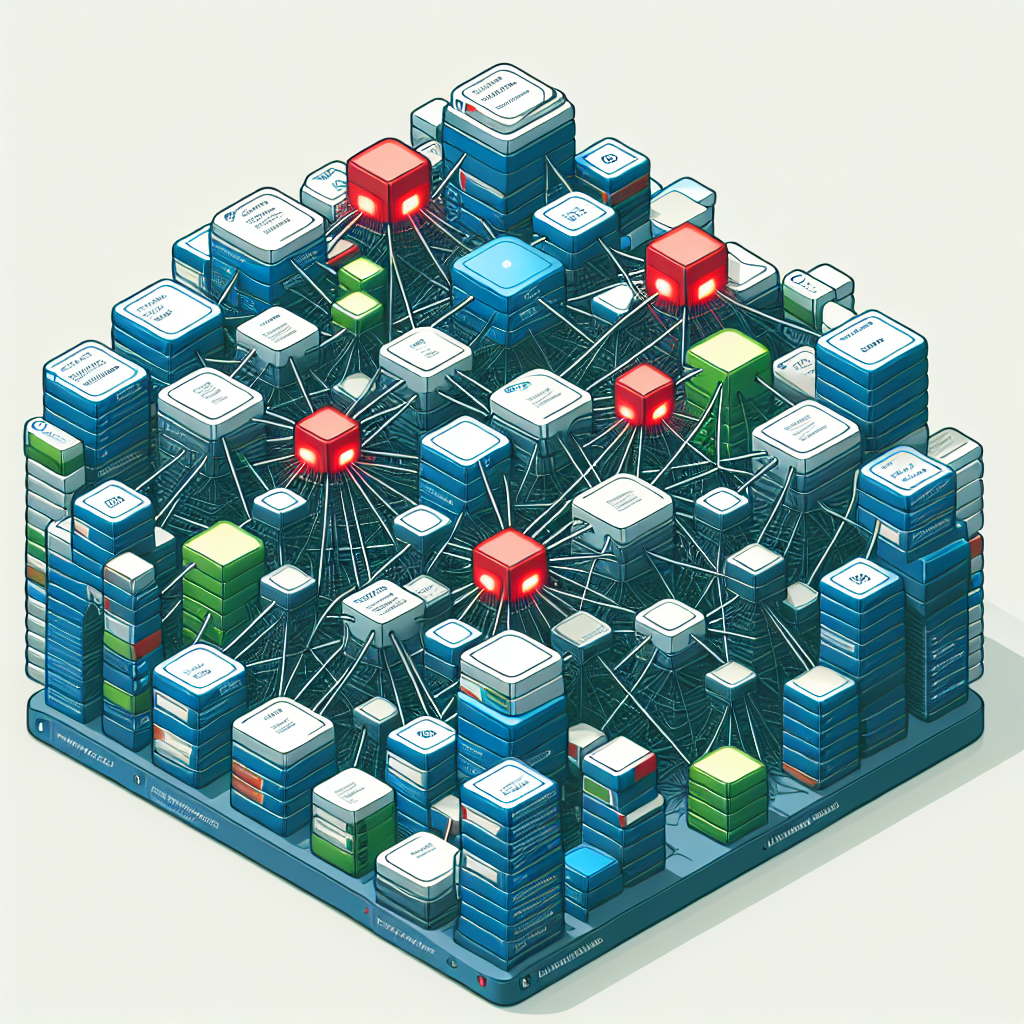
The Senior Developer's Security Awakening: Why "Vibes-Based" Coding Is Finally Meeting Its Match
You know that senior developer on your team — the one who's been shipping code since jQuery was revolutionary?
They can architect a distributed system in their sleep, but ask them about Content Security Policies and watch their eyes glaze over.
They're not alone. An entire generation of senior developers built their careers when "security" meant adding a login form and calling it a day.
Now these same developers are suddenly responsible for defending against supply chain attacks, zero-days, and AI-powered vulnerability scanners.
The memes flooding Reddit aren't just funny — they're a cry for help from developers who realize their "it works on my machine" mentality doesn't cut it anymore.
The Great Security Gap Nobody Talks About
Most senior developers entered the industry between 2005 and 2015, a golden age when frameworks were simple and Stack Overflow had answers to everything.
Security was someone else's problem — usually a mysterious team that showed up once a year to run a penetration test.
These developers learned to code when the biggest security concern was SQL injection, and even that was mostly handled by using prepared statements. HTTPS was optional.
CORS was annoying. Authentication meant sessions and cookies.
Fast forward to 2024. The average web application now includes 1,000+ dependencies.
A single `npm install` can introduce vulnerabilities from packages you've never heard of, maintained by anonymous contributors halfway across the world.
The attack surface has exploded exponentially.
Modern applications face threats from compromised dependencies, prototype pollution, server-side request forgery, and dozens of vulnerability classes that didn't exist when many senior developers were learning their craft.
Yet most senior developers are still coding like it's 2012. They trust their instincts, their experience, their "vibes" about whether code looks secure.
They've shipped hundreds of features without major incidents, so why change now?
This approach worked when applications were simpler and attacks were less sophisticated. Today, it's a ticking time bomb.
When Seniority Becomes a Liability
The Reddit threads tell the real story. Senior developers sharing their shock at failing security audits.
Team leads admitting they don't understand half the vulnerabilities flagged by their scanning tools. Architects designing systems with fundamental security flaws they never learned to recognize.
One viral post described a senior developer with 15 years of experience who didn't know what CSRF tokens were.
Another shared how their entire team of senior engineers had been storing API keys in their React app's environment variables, visible to anyone who opened developer tools.
These aren't bad developers. They're experienced professionals who've been incredibly successful building features and solving business problems.
But the industry evolved faster than their security knowledge.
The "vibe-based" approach to security — where you rely on intuition and past experience — fails catastrophically in modern development. You can't intuit whether a dependency has been compromised.
You can't guess if your JWT implementation is vulnerable to algorithm confusion attacks.
What makes this especially challenging is that senior developers are often the ones making architectural decisions.
They're choosing frameworks, designing APIs, and setting patterns that junior developers follow.
When they lack security knowledge, it cascades through entire organizations.
The New Security Reality Developers Face
Modern web security isn't just about preventing SQL injection anymore. Consider what developers must now understand:
**Supply Chain Security**: The average Node.js application has over 1,000 transitive dependencies. Each one is a potential attack vector.
The recent `polyfill.io` incident affected 100,000+ websites when a single CDN was compromised.
**Client-Side Attacks**: XSS has evolved far beyond `alert('hacked')`. Modern attacks use sophisticated payload delivery, bypass CSP headers, and persist through framework updates.
React's `dangerouslySetInnerHTML` isn't just a bad practice — it's an invitation for disaster.
**API Security**: GraphQL introduced new attack surfaces many developers don't understand. Rate limiting, query depth limiting, and field-level authorization are essential but often ignored.
**Authentication Complexity**: OAuth 2.0, OIDC, WebAuthn, passkeys — modern authentication is orders of magnitude more complex than the session-based auth many senior developers grew up with.

**Infrastructure as Code**: Misconfigured Terraform can expose entire cloud infrastructures. One wrong IAM policy and your S3 buckets are public.
Yet many senior developers treat IaC like application code, without understanding the security implications.
The memes about "senior vibe coders" aren't mocking incompetence — they're highlighting how the industry failed to bring experienced developers along as security requirements exploded in complexity.
Why Traditional Learning Approaches Fail
Senior developers face unique challenges when learning security. They can't just take a bootcamp or watch YouTube tutorials designed for beginners.
They need to retrofit security knowledge into years of established patterns and habits.
The typical security resources are either too basic ("here's what XSS is") or too specialized ("implementing post-quantum cryptography in Rust").
There's little content for experienced developers who need to quickly level up their security knowledge while still shipping features.
Many senior developers also face the psychological barrier of admitting knowledge gaps.
After years of being the expert everyone turns to, it's uncomfortable acknowledging you don't understand modern security practices.
Some try to compensate by adding security tools without understanding them.
They install Snyk, enable GitHub's Dependabot, add a WAF — but without understanding what these tools do, they're just adding complexity without real protection.
The result is security theater.
Applications that look secure on paper but are fundamentally vulnerable because the developers implementing security features don't understand the threats they're defending against.
Building Security Intuition That Actually Works
The solution isn't to send every senior developer to security bootcamp. It's to build security thinking into their existing workflow and expertise.
Smart organizations are taking a different approach.
Instead of treating security as a separate discipline, they're integrating it into the development process in ways that leverage senior developers' strengths.
**Threat Modeling During Design**: Senior developers excel at system design. Teaching them to threat model during architecture reviews turns their design skills into security assets.
They're already thinking about edge cases — now they're thinking about attack vectors.
**Security Champions Programs**: Rather than making everyone a security expert, organizations are identifying senior developers who show interest and giving them additional training.
These champions become bridges between security teams and development teams.
**Automated Security Feedback**: Tools like Semgrep and CodeQL provide security feedback in the IDE, where developers are already working.
This turns security learning into a continuous process rather than a one-time training event.
**Pair Programming with Security Engineers**: Nothing beats learning by doing. Pairing senior developers with security engineers on actual vulnerabilities teaches practical skills that stick.
The key is making security knowledge contextual and immediately applicable.
Senior developers don't need to become penetration testers — they need to understand security well enough to make good decisions in their daily work.
What's Coming Next
The industry is at an inflection point. The gap between security requirements and developer knowledge isn't sustainable.
We're seeing the emergence of several trends that will reshape how developers approach security.
**AI-Powered Security Tools**: The next generation of security tools won't just flag vulnerabilities — they'll explain them in context and suggest fixes.
GitHub Copilot already helps write secure code patterns.
Future tools will act like pair programmers who happen to be security experts.
**Shift-Left Security**: Security is moving earlier in the development process. Instead of finding vulnerabilities in production, developers will get immediate feedback while coding.
This continuous security education will gradually build intuition.
**Security-First Frameworks**: Frameworks are increasingly making secure patterns the default.
Next.js's built-in CSRF protection, Remix's automatic escaping, and SvelteKit's CSP headers remove entire classes of vulnerabilities without developers having to think about them.
**Mandatory Security Certification**: Some organizations are already requiring security certifications for senior roles.
This trend will likely accelerate as breaches become more costly and regulations become stricter.
The "senior vibe coder" meme represents a transitional moment. The industry is acknowledging that experience alone isn't enough anymore.
But rather than dismissing senior developers, we need to help them evolve.
The developers who embrace this change — who add security to their expertise — will become even more valuable. Those who don't risk becoming liabilities, no matter how much experience they have.
Security isn't optional anymore. It's not a specialty.
It's a core competency every developer needs, regardless of seniority. The vibes-based approach had a good run, but it's time for something more robust.
The good news? Senior developers have already proven they can learn and adapt.
They survived the transition from desktop to web, from monoliths to microservices, from waterfall to agile. Adding security to their toolkit is just the next evolution.
The memes will fade, but the underlying message will stick: in modern development, security knowledge isn't a nice-to-have — it's table stakes.
---
Story Sources
r/webdevreddit.com
From the Author
TimerForgeTrack time smarter, not harderBeautiful time tracking for freelancers and teams. See where your hours really go.Learn More →
AutoArchive MailNever lose an email againAutomatic email backup that runs 24/7. Perfect for compliance and peace of mind.Learn More →
CV MatcherLand your dream job fasterAI-powered CV optimization. Match your resume to job descriptions instantly.Get Started →
Hey friends, thanks heaps for reading this one! 🙏
If it resonated, sparked an idea, or just made you nod along — I'd be genuinely stoked if you'd show some love. A clap on Medium or a like on Substack helps these pieces reach more people (and keeps this little writing habit going).
→ Pythonpom on Medium ← follow, clap, or just browse more!
→ Pominaus on Substack ← like, restack, or subscribe!
Zero pressure, but if you're in a generous mood and fancy buying me a virtual coffee to fuel the next late-night draft ☕, you can do that here: Buy Me a Coffee — your support (big or tiny) means the world.
Appreciate you taking the time. Let's keep chatting about tech, life hacks, and whatever comes next! ❤️